Characteristics:
- Title: Penetration testing Azure for ethical hackers
- Authors: Davide Okeyode & Karl Fosaaen
- Edition: Packt
- First publication date: September 2021
- Price (as of 06/05/2022): 45,03€ (Amazon)
- Pages: 332 (320 of technical content)
Outline
Outline of the book is available on Packt’s website.
It goes like this:
- Chapter 1: Azure Platform and Architecture Overview
- Chapter 2: Building Your Own Environment
- Chapter 3: Finding Azure Services and Vulnerabilities
- Chapter 4: Exploiting Reader Permissions
- Chapter 5: Exploiting Contributor Permissions on IaaS Services
- Chapter 6: Exploiting Contributor Permissions on PaaS Services
- Chapter 7: Exploiting Owner and Privileged Azure AD Role Permissions
- Chapter 8: Persisting in Azure Environments
Each chapter is around 50 pages, a bit less for the first and last ones. The book is nicely cut into sections of that size, making it easier to study and not indigest.
I recommend reading it in the chapter’s order, as there are concepts and references in the last chapters that depends on the ones seen previously. The chapters are organized in a way that looks like a penetration testing methodology: from the least privileged user in the cloud to the highest and towards persistence afterwards.
The book includes hands-on exercises for which a penetration virtual machine and other hosts need to be deployed into an Azure tenant.
Issues with ressources allocation
I ran into issues for the allocation and the deployment of both the pentest virtual machine and the hosts used in the exercises section of the book with the free Azure plan (200€ offered). Specifically, no VM were available in the zones described in the book. Here is how I got around it:
- allocate the pentest VM on any available location, turned out to be Japan East for me.
- allocate the exercises in any available location other than the one from above, turned out to be East Asia.
- for each ps1 exercise script, modify the
locationvariable with the location from above (e.g.eastasia)
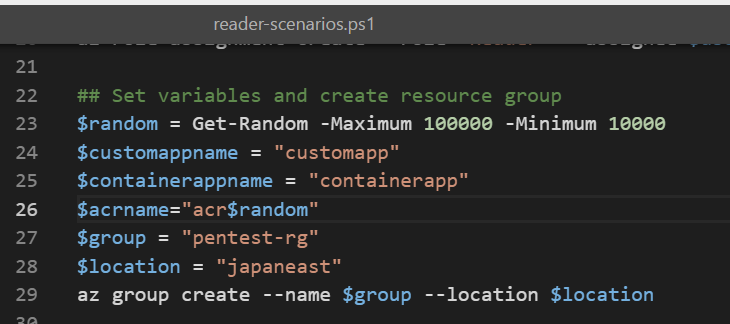
And then everything worked as expected.
Issues with the hands-on exercises
Overall, I ran into very few issues with the hands-on exercises. I am letting the below here for whoever would be reading the book and is trying to debug what is going on:
Chapter 7 labs
The setup script was not working due to the non-assignment of the global administrator role to the demo user. I made a pull request for it but you can circumvent it by manually adding the role to the user in the Azure portal.
Chapter 8 labs
I had to follow https://stackoverflow.com/questions/43323123/warning-unable-to-find-module-repositories to install the Az module and make it work on the victim’s VM.
Overall opinion
I found the book instructive and well written. I had a little experience with Azure security beforehand but that is not necessary for the read, even if I would recommend it. You can gain that knowledge going through Microsoft documentation for free.
The biggest value of the book is the methodology given and the description of precise attacks with hands-on exercises in my opinion. The methodology is not something you are going to find through any documentation and if you are a freelance worker without access to mentors or just someone without first hands-on experience, I feel like this can fill some gaps.
The attacks are still all relevant as of today (all tested) and you get a practical approach towards it with the hands-on exercises. I can only recommend to do them all, even some that looks trivial, as a few details are only obvious when doing and not only reading.
For each of these, there are recommendation for mitigation/detection and you can feel that the authors are not only writing from an offensive point of view, which I believe to be a good thing.
Regarding the time of study/reading I made it through in three weeks, mostly 1-3 hours per day on evenings and weekends. It really depends on your rythm, but I got hooked up by the book at Chapter 3 and after that, I could not stop.
Conclusion
If you are willing to dive into Azure’s security as a penetration tester and are looking for material, this is a good reference. I would not say it is a bible but a good starting point into Microsoft’s cloud environment attacks and defences.
Kudos to David Okeyode (@asegunlolu) and Karl Fosaaen (@kfosaaen) for writing good quality material.
